Another Locky email campaign
The new campaign was discovered by App River. Potentially 23 million of emails were sent with subjects such as ‘please print’, ‘documents’ and ‘scans’ in an effort to spread Locky ransomware.
As with all Phishing campaigns end user education is your best defense. With this number o emails, even if it is overestimated by 90% there will be significant numbers of users caught but it and they potentially will send more mail messages.
Security updates released for Adobe Flash Player
Adobe has identified multiple vulnerabilities for versions of Flash Player on Windows, Mac, Linux and Chrome OS. They are listed as Critical and users should apply updates ASAP.
Source: Adobe
Oracle Patches 270 Vulnerabilities
Oracle has released the first Critical Patch Update of 2017. Oracle is patching 270 different vulnerabilities. Oracle strongly recommends that organizations patch quickly.
Check for your products Here
Security update for Firefox 49
Mozilla has released an update for Firefox 49 with eighteen fixes, four of which are listed as Critical including a highly scrutinized flaw in its automated update process for add-ons in Firefox, specifically around the expiration of certificate pins. The vulnerability allowed the interception of browser traffic which could lead to remote code execution.
Adobe Security Bulletin:CVE-2016-1019
Adobe released an updated security advisory earlier this week regarding a critical vulnerability that exists in Adobe Flash Player 21.0.0.197 and earlier versions. This vulnerability affects Windows, Macintosh, Linux, and Chrome OS and could cause the browser to crash or possibly allow for remote code execution, Adobe has introduced in Flash Player 21.0.0.182 a mitigation that protects users against attackers that attempt to exploit this vulnerability, but during today, the company is expected to release a security update. Users are advised to upgrade Flash Player in the moment a new update is released, and in case they haven’t done this yet, they can go to the Adobe Flash Player Download Center and download the software from there, and install it in each browser.

New Crypto threat: Petya Ransomware
Petya represents is new twist on crypto. It was found recently targeting companies in a spam campaign. The emails contained a link to a Dropbox file that if clicked loads a dropper that installs Petya. Dropbox has since removed the link and several others that were associated that also contained the same malware.
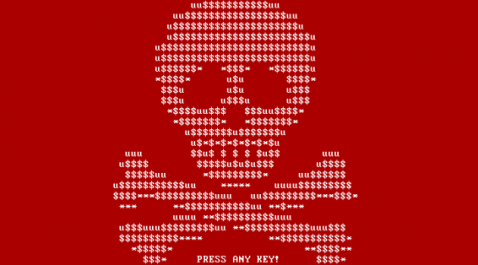
If the archive is downloaded and executed, the ransomware is installed. Petya does not encrypt the file data itself, which would take a long time for an entire hard drive, but by encrypting the MFT the OS will no longer know where the files are located on disk. Then the malicious program will trigger a critical Windows error that will cause the computer to reboot — a condition known as a Blue Screen of Death (BSOD).