Another Locky email campaign
The new campaign was discovered by App River. Potentially 23 million of emails were sent with subjects such as ‘please print’, ‘documents’ and ‘scans’ in an effort to spread Locky ransomware.
As with all Phishing campaigns end user education is your best defense. With this number o emails, even if it is overestimated by 90% there will be significant numbers of users caught but it and they potentially will send more mail messages.
Security Update for Microsoft Malware Protection Engine
Microsoft has released an update to the Microsoft Malware Protection Engine addressing a security vulnerability. The update addresses a vulnerability that could allow remote code execution if the Microsoft Malware Protection Engine scans a specially crafted file. An attacker who successfully exploited this vulnerability could execute arbitrary code in the security context of the LocalSystem account and take control of the system.
Users should run their Microsoft updates ASAP and apply the patch if using one of the Microsoft Provided Malware products such as the Windows Defender line.
Jigsaw Ransomware: Deletes files
The Jigsaw crypto malware may be propagated online via corrupted archive files, text and PDF documents that are attached to spam mail. Emails may appear to come from an internal source or an outside vendor and you should be cautious when receiving invoices because they may be targeted with a spear phishing designed to bypass safe email practices.
The Jigsaw Trojan may disguise itself as an instance of Mozilla Firefox and display a program window that features an animated ransom note that is accompanied by a doll that you might have seen in the movie Saw from 2004. Jigsaw Ransomware prompts the victim to send a payment of 0.4 Bitcoins to receive a decryption key

United States, Canada Issue Joint Alert on Ransomware
We dedicate a lot of time to educating our clients to the dangers of Ransomware. Given exactly how devastating the impact can be from one infection and the fact that it is often successful due to human error.
This week the United States Department of Homeland Security (DHS), in collaboration with Canadian Cyber Incident Response Centre (CCIRC), is releasing an alert regarding Ransomware. This is how serious the situation is becoming. Every company needs to educate their system users about Ransomware and how to avoid infections.
Source: US-CERT

New Crypto threat: Petya Ransomware
Petya represents is new twist on crypto. It was found recently targeting companies in a spam campaign. The emails contained a link to a Dropbox file that if clicked loads a dropper that installs Petya. Dropbox has since removed the link and several others that were associated that also contained the same malware.
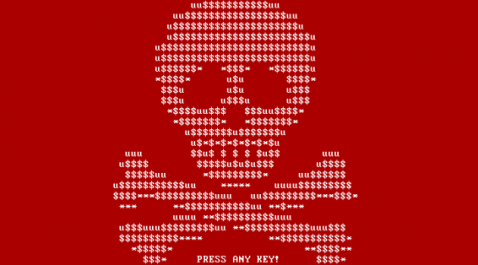
If the archive is downloaded and executed, the ransomware is installed. Petya does not encrypt the file data itself, which would take a long time for an entire hard drive, but by encrypting the MFT the OS will no longer know where the files are located on disk. Then the malicious program will trigger a critical Windows error that will cause the computer to reboot — a condition known as a Blue Screen of Death (BSOD).
New Ransomeware Encrypts files on unmapped shares
Up until now Cryptolocker / ransomware has encrypted local files and files locates on remote machines that are mapped to the infected workstation.
A new ransomware has been discovered called Locky that encrypts your data using AES encryption and then demands .5 bitcoins to decrypt your files. It targets a large amount of file extensions and even more importantly, encrypts data on unmapped network shares. Like CryptoWall, Locky also completely changes the filenames for encrypted files to make it more difficult to restore the right data.
Locky is being distributed via email, one method being attaching Word documents containing ATT: Invoice and messages such as “Please see the attached invoice”.
Locky Decrypter Page:

Security: CryptoWall 4.0 in the wild
The fourth version of the CryptoWall ransomware has landed in the wild, equipped with better evasion techniques and tactics to thwart antivirus protection and detection.
Ransomware attacks computers and encrypts user files and folders via infected email attachments, with attackers demanding ransom payments to unlock the scrambled documents.
Users are told to make the payment by a specific deadline or risk having the private key to unlock the files deleted.
The active CryptoWall ransomware spawned from CryptoLocker, which is thought to have extorted more than $3 million from victims before the botnet used to distribute it – Gameover Zeus – was taken down last year.
To avoid getting caught by CryptoWall, we recommended keeping systems up to date, maintain regular backups and educating users to avoidin emails with attachments sent by unknown senders, and using products that can detect and block recent ransomware variants.
Ransomware attacks up 113 Percent in 2014
Beginning in 2013 a new type of Malware was spreading via email: Ransomware. Even today in 2015 most people are unaware of Ransomware and are unable to take steps against it.
As the name implies, “ransomware” is malware that prevents you from accessing data or information on your computer until you pay a ransom or a specified amount of money.
Just as sophisticated phishing emails appear to be from trusted financial institutions or other respected companies, ransomware can appear to be from legitimate sources such as legal authorities or even government officials. A demand is usually made for a fine to be paid for the “illegal activity” that was supposedly found originating from your computer. The illegal activity claim could be items like copying songs or duplicating videos and violating copyright laws.
The two commonest forms of ransomware will: lock the screen with a full-screen image or Web page to prevent access to the computer; or encrypt files with a password that prevents access to data or information.
The other bad news for those infected with this malware is that paying the ransom does not always return your computer to normal.
Source: Symantec
Curve-Tor-Bitcoin (CTB) Locker ransomware Alert
A variant of Curve-Tor-Bitcoin (CTB) Locker ransomware is being distributed in a spam campaign now offers victims additional time to pay the ransom, but also requires them to pay a whole lot more than previously, according to the latest research by Trend Micro. This is just the latest wave of this type of malware and users need to be vigilant.
The bad news is that, as its name implies, ransomware holds your system ransom. The first thing this package does is corrupt your files – all your files. Photos, videos, office documents; Local files, network files, shared files… Then a warning screen from the criminals alerts you, telling you that your files are “encrypted” and demanding that you pay a ransom via electronic fund transfer or your files will be lost forever.
Source: Trend Micro
