WCry Ransomware Using NSA Exploit Leaked by Shadow Brokers running wild
Today security experts are warning of the continued spread of WCry and of numerous variants being released over the weekend.
Typical of Any Ransomware users should be vigilant with any emails that could be carrying a payload or be links to a payload. At this point Microsoft has not ruled out any attack vectors:
We haven’t found evidence of the exact initial entry vector used by this threat, but there are two scenarios we believe are highly possible for this ransomware family:
- Arrival through social engineering emails designed to trick users to run the malware and activate the worm-spreading functionality with the SMB exploit
- Infection through SMB exploit when an unpatched computer can be addressed in other infected machines
Microsoft has released a patch for Operating systems going as far back as XP:
Windows update MS17-010
New Locky campaign underway
Ransomware continues to be among most insidious threats facing computer users this year. Researchers have recently observed a spike in Locky Ransomware phishing. The most recent campaign uses emails with the subject Re:

The Locky ransomware encrypts files renaming the to [unique_id][identifier].locky. The malware will also delete all of the copies of documents in the Shadow Volume, making impossible to restore files.
The only real defenses against these types of attacks is user education and a solid backup plan.
New ransomware BadBlock released
A new ransomware called BadBlock has been released. BadBlock encrypts your data and then requests 2 bitcoins to get your encryption. When it encrypts your files it does not append a special extension to the files.
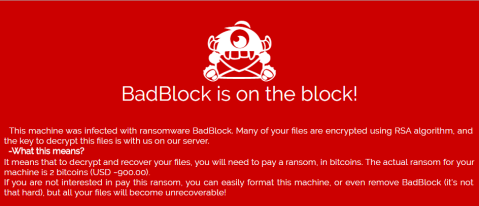
The most common way of distributing the BadBlock Ransomware is through corrupted email messages that contain corrupted embedded links or file attachments. When computer users open the content included in the email message, the BadBlock Ransomware runs on the victim’s computer encrypting files.
CryptXXX 2.0 – Decryption tool ineffective
A new version of CryptXXX has been released which defeats the free decryption tool that Kaspersky released last week. With the speed variations and updates are being released getting a Crypto virus is still very much a restore situation and you should have a plan in place.
Crypto payment options expanding
Two news ransomware products have been released, the first called TrueCrypter,encrypts your data using AES-256 encryption and then demands either .2 bitcoins or $115 USD in Amazon gift cards. The second called Alpha Ransomware encrypts your data with AES-256 encryption and then demands $400 USD in the iTunes Gift Cards.
This is another sign of how common Ransomware is becoming. As more people are infected it is effecting users who lack the knowledge to obtain Bitcoins and more payment methods are needed.
Jigsaw Ransomware: Deletes files
The Jigsaw crypto malware may be propagated online via corrupted archive files, text and PDF documents that are attached to spam mail. Emails may appear to come from an internal source or an outside vendor and you should be cautious when receiving invoices because they may be targeted with a spear phishing designed to bypass safe email practices.
The Jigsaw Trojan may disguise itself as an instance of Mozilla Firefox and display a program window that features an animated ransom note that is accompanied by a doll that you might have seen in the movie Saw from 2004. Jigsaw Ransomware prompts the victim to send a payment of 0.4 Bitcoins to receive a decryption key

United States, Canada Issue Joint Alert on Ransomware
We dedicate a lot of time to educating our clients to the dangers of Ransomware. Given exactly how devastating the impact can be from one infection and the fact that it is often successful due to human error.
This week the United States Department of Homeland Security (DHS), in collaboration with Canadian Cyber Incident Response Centre (CCIRC), is releasing an alert regarding Ransomware. This is how serious the situation is becoming. Every company needs to educate their system users about Ransomware and how to avoid infections.
Source: US-CERT

New Crypto threat: Petya Ransomware
Petya represents is new twist on crypto. It was found recently targeting companies in a spam campaign. The emails contained a link to a Dropbox file that if clicked loads a dropper that installs Petya. Dropbox has since removed the link and several others that were associated that also contained the same malware.
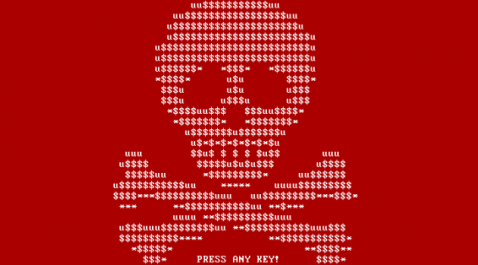
If the archive is downloaded and executed, the ransomware is installed. Petya does not encrypt the file data itself, which would take a long time for an entire hard drive, but by encrypting the MFT the OS will no longer know where the files are located on disk. Then the malicious program will trigger a critical Windows error that will cause the computer to reboot — a condition known as a Blue Screen of Death (BSOD).
New Ransomeware Encrypts files on unmapped shares
Up until now Cryptolocker / ransomware has encrypted local files and files locates on remote machines that are mapped to the infected workstation.
A new ransomware has been discovered called Locky that encrypts your data using AES encryption and then demands .5 bitcoins to decrypt your files. It targets a large amount of file extensions and even more importantly, encrypts data on unmapped network shares. Like CryptoWall, Locky also completely changes the filenames for encrypted files to make it more difficult to restore the right data.
Locky is being distributed via email, one method being attaching Word documents containing ATT: Invoice and messages such as “Please see the attached invoice”.
Locky Decrypter Page:

Security: CryptoWall 4.0
Cryptolocker began circulating in 2013, with variants coming soon after. Designed to infect, encrypt and then ransom it has been shockingly effective. The typical infection vector of attack is phishing because the average user has proven to be susceptible to this type of attack.
These attacks begin with a zip file email attachment. Inside the zip is what appears to the user as a PDF/doc/text attachment, but this is actually the initial dropper. Once launched, this will silently drop an executable in a random temp or appdata. This will be what communicates to the command and control sever – which will then take information about your PC that’s already been gathered and then based on that info, drop the appropriate ransomware, pre-built for your PC environment.
The most significant change in CryptoWall 4.0 is that it now also encrypts the filenames of the encrypted files. Each file will have its name changed to a unique encrypted. The filenames are encrypted to make it more difficult to know what files need to be recovered.
We cannot stress enough how important managing email attachments is. At this point in time we recommend all clients regardless of size ensure there is more than a simple email policy in-place, that they have an active software based solution scanning their messages and limiting the exposure to mail based attacks.