Personal Mobile Devices with access to corporate networks should be secured
Your employees phone and or tablet more than likely has access to their corporate email account. In many cases they have access to corporate documents in the cloud or via VPN.
The simple act of enabling a password or PIN number on a phone can save you a tremendous amount of hassle. This is the simplest front line of defense. While people don’t deliberately forget their phone in a public restroom, gym, or restaurant, we all know it happens. So, make sure you have the appropriate device lock in place, either a pin code, or screen pattern lock. If you have a pattern lock (this is where you join the dots to unlock your phone) make sure you wipe the screen to avoid leaving smudges that can reveal your pattern. (We actually recommend not using a pattern lock for this reason).
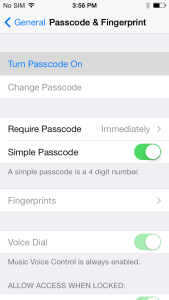 On iOs (Varies slightly by version) Click on Settings, General and Passcode Lock (you may have to scroll down a bit). This will bring you to the Passcode Lock menu, although if you already have a PIN or password set, you’ll have to input it first.
On iOs (Varies slightly by version) Click on Settings, General and Passcode Lock (you may have to scroll down a bit). This will bring you to the Passcode Lock menu, although if you already have a PIN or password set, you’ll have to input it first.
Turn Passcode On is the first and most tempting option here, but don’t click on it yet. First, you have to make a decision: Do you want a four-digit PIN, or a more complex alphanumeric password? If four digits suit you fine, ensure that Simple Password is turned on. If not, leave it off.
Although a PIN has fewer characters than a password, it’s generally just as hard for a casual thief to guess.
While a four-digit PIN has only 10,000 possible combinations, a long alphanumeric password of 10 or more digits that includes upper- and lowercase letters, numbers and punctuation marks will have trillions.
 Android can be a bit more complex as there are an almost endless variety of devices with vendor specific “skins” and security settings. Generally however you will find a setting called Lock Screen under settings.
Android can be a bit more complex as there are an almost endless variety of devices with vendor specific “skins” and security settings. Generally however you will find a setting called Lock Screen under settings.
Important to note with Android; there are many lock screen replacements available and many include their own lock methods. There are programs that run and many can be circumvented more easily than the operating systems locks and their locks should be avoided.